Nowadays, every individual using the internet leaves various records and traces under the form of a digital footprint. However, do we always need ‘to step’ before leaving marks? Apparently, not. 81% of children under two currently have some kind of digital dossier or footprint, with images of them posted online (Singer, 2013). The wider context is explained by Alec Couros in this video.
Real-world and the online identities are very different from each other (Internet Society, 2013). Composed of partial identities, profiles and personas the online identities can induce the idea of a parallel life. Couros legitimately asks: ‘Should we teach our children as though they have two lives, or one?’. My answer is no, but social media seems to conduct people in this direction.
It was! The matter of being yourself online was addressed by Casey Neistat, co-founder of Beme – company recently purchased by CNN. Along with his team, he created an app where you could share your life as it is. No filters, no versions of who we are. Not seeing the world through your phone, but seeing the world through your eyes.
This concept is unique because it established a network by building a bridge between social media and real life. I would like to see it further developed by other online platforms where we create profiles, creating more accurate versions of our online identities.

Building up on the point made earlier, creating sockpuppets online became easier than ever and this led to the birth of false identities on the internet (Seife, 2014). The justification is described in the following infographic and supported by a few examples.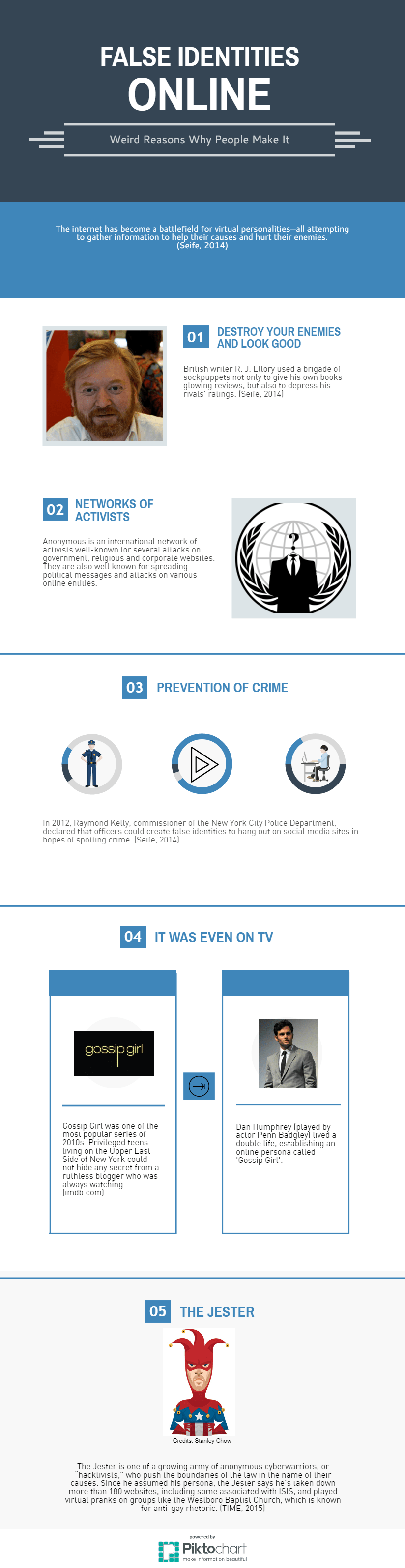

Sharing information online, voluntary (social media) or involuntary (online advertising companies), people can often become victims of phishing (Internet Society, 2013). The method is briefly described in the following infographic.
Another security concern is related to passwords. Recently, over 1bn of Yahoo’s clients were compromised by the biggest data breach in history. This was relevant because password sharing between websites became very common for a lot of users (Thielman, 2017). In order to avoid being the victim of this, follow the tips in the presentation below.

The online presence became a thing difficult to manage. As Krotoski’s article (2012) describes two different approaches, we can divide once again the users of internet in two categories: anonyms and authentic identities. My post presents both: pros and cons for having multiple online identities. However, convenience seems to be the selling point for it, but do you want to see the world through your phone or your eyes?
426 words
Sources:
Couros, A. (2015) Identity in a digital world | Alec Couros | TEDxLangleyED. YouTube. Available from: https://www.youtube.com/watch?v=pAlIBTgYfDo [Accessed 24 February 2017].
Internet Society (2013) Privacy & identity. Available from: http://www.internetsociety.org/what-we-do/internet-technology-matters/privacy-identity [Accessed 24 February 2017].
Krotoski, A. (2012) Online identity: Is authenticity or anonymity more important? The Guardian, 19 April. Available from: https://www.theguardian.com/technology/2012/apr/19/online-identity-authenticity-anonymity [Accessed 24 February 2017].
Morris, C. (2011) 14 identity theft methods used by criminals. Available from: http://patch.com/california/montrose/14-identity-theft-methods-used-by-criminals [Accessed 24 February 2017].
Perlberg, S. (2016) CNN buys Casey Neistat’s video App Beme. Available from: https://www.wsj.com/articles/cnn-buys-casey-neistats-video-app-beme-1480353128 [Accessed 24 February 2017].
Seife, C. (2014) Android can’t compete with iMessage. Google is changing that. Available from: https://www.wired.com/2014/07/virtual-unreality-the-online-sockpuppets-that-trick-us-all/ [Accessed 24 February 2017].
Singer, D. (2013) How technology has changed childhood – Ten stats. Available from: http://www.futurelab.net/blog/2012/05/how-technology-has-changed-childhood-%E2%80%93-ten-stats [Accessed 24 February 2017].
Thielman, S. (2017) Yahoo hack: 1bn accounts compromised by biggest data breach in history. The Guardian, 21 February. Available from: https://www.theguardian.com/technology/2016/dec/14/yahoo-hack-security-of-one-billion-accounts-breached [Accessed 24 February 2017].
TIME (2015) These are the 30 most influential people on the Internet. Available from: http://time.com/3732203/the-30-most-influential-people-on-the-internet/ [Accessed 24 February 2017].


Hi Andrei, I really enjoyed your blog post this week, especially as it made effective use of visuals, allowing you to provide a variety of content within the word count. Your pictogram of ‘False Identities Online, Weird Reasons Why People Make It’, was both refreshing and informative, highlighting the positive and negative role of multiple identities; I hadn’t considered the use of false identities by police officers in the prevention of crime.
I was also intrigued by your exploration of Beme, however, found some criticisms in its concept. I agree that online versions of ourselves often don’t resemble reality, but even as users of Beme don’t record their face and instead record what they are doing, they are still able to present an unauthentic self by selecting the activities they want others to see. To me it feels like a version of Snapchat with even less authenticity as their face is rarely displayed but the selective element remains? I’d be interested to hear your thoughts!
Word count: 165
LikeLiked by 1 person
Hi Scott!
Thank you very much for your comment, greatly appreciated. I am happy to see that you sympatised with the visuals. In regards with your question, I found it very interesting and I actually asked myself the same thing some time ago.
In some way I agree with you, people can use Snapchat the same way Beme works, but very often the users abuse of the use of filters and texts. I think that Beme stands out for me, making posted content more genuine because if we refer to social media as a three steps cyclical process, Content -> Response -> Edit (as in this video: https://www.youtube.com/watch?v=-JcvD1gLjSM), Beme is just a 2-step process: Content -> Response. It’s about the fact that the app doesn’t give you a choice of being genuine or not. Also the issue of not displaying the face can be addressed by using your finger to cover the proximity sensor of the device and film yourself.
Hope I managed to answer your question!
Thanks again for your comment,
Andrei
LikeLike
Hi again!
Upon reflection, I can see how removing the editing process from the cycle is the key feature of the app and of sharing content, thus creating greater authenticity. I also watched a few more vids on the subject and came to enjoy the ‘see the world through your eyes’ aspect of Beme that you and others have mentioned. Whilst it is impossible to be truly authentic through sporadic posting on social media – as snapshots of life can never be truly representative – I can see how Beme minimizes the creation of unauthentic identities as it restricts users from trying over and over again to present the ‘best’ version of themselves.
Thanks for introducing me to the app!
LikeLiked by 1 person
Hi again Scott!
I am glad that the mentioned aspects make more sense to you now! You are definitely right with the fact that it’s impossible to be truly authentic on social media. Even more than this, I consider that this fact is backed by the ‘failure’ of Beme, which doesn’t exist anymore as an app. However, the team behind it is now working for CNN under the same name: Beme, as an independent technology company. Thereby, I think that the fact that they were purchased by the media giant is a confirmation of their success. More about their journey can be found on their website: https://beme.com/
Thanks your comments!
Andrei
LikeLike
I have read around Beme and it’s a shame to hear the app ended, although good to hear they are now working on further projects which hopefully may continue to consider authenticity as point of discussion!
Once again, thanks for introducing me to Beme!
LikeLiked by 1 person
Hi Andrei,
Thank you for a great read! I loved your use of visuals, they made your points easy to understand and enjoyable to read. I especially liked the infographic on false online identities; your varied examples and the accompanying case studies helped me better link your points to other real world scenarios.
To answer your question at the end, my answer is my eyes. I appreciate the way online communities help us connect with people in a large scale, however it’s really upsetting to see people constantly on their phones instead of appreciating their surroundings – do you agree? Consequently I always make sure that when I capture memories (e.g. on holiday) I post them after i’ve completed my experience so that I make the most of the moment and not spend my time editing a post.
It would of been interesting to learn abit about your personal experience; do you consider yourself to be authentic or anonymous?
Eloane
(160)
LikeLiked by 1 person
Hi Ellie,
Thank you very much for your kind comment. Related to people constantly on their phones instead of appreciating their surroundings, I definitely agree with your point. It is sad to see them not making the most of the moment because they see it through their phones. However, I sometimes want to keep some memories with me forever. That’s when I use my phone to capture moments that I want to always remember, with the risk of not making the most of the actual moment… Maybe Google Glasses are the solution to this? 🙂
I think that posting content after completing an experience in order to avoid spending time editing a post is a smart thing and it definitely contributes to living an enhanced experience.
Related to your final question, I think that I am more authentic than anonymous. I openly share my thoughts when I think that they need to be shared and I do it in an authentic way, by doing it from personal accounts, linked to my real name and personal details.
Thanks again for your comment!
Andrei
LikeLiked by 1 person